Last change: December 21st 2021. Thanks to Dirk Bautz!
Last change: December 21st 2021. Thanks to Dirk Bautz!
This is the 2nd part to my article “Which ciphers to use on a Citrix ADC /NetScaler?” This one had been about TLS versions up to 1.2 only.
Moving from TLS 1.2 to TLS 1.3 on an existing Citrix ADC ( NetScaler) may be a big step with some obstacles to overcome. It needs some investigation.
Why TLS 1.3?
Simple: TLS 1.3 is faster, as it uses less packets to set up the session. So it sends content faster to the user. It also uses less CPU than TLS 1.2. TLS 1.3 also eliminated several weaknesses as it removes several backward-compatibility functions. TLS 1.2 won’t get adapted any more, all new enhancements will go to TLS 1.3 only.
Last not least: HTTP QUIC / HTTP 3 will only work with TLS 1.3.
The problem?
It seems to be easy: Just tick the TLS 1.3 checkbox, that’s it.
It’s not. It won’t work. All connections will still be TLS 1.2, or, even worse, connections may fail. My college Dirk Bautz didn’t agree, he was able to just enable TLS 1.3 successfully, but I had been not. We had a debate about it. He proved, he was right (but I’m not an idiot, so there must have been something!)
 The reason is: If you use SSL profiles, Citrix ADC / NetScaler will not allow TLS 1.3. It would work, if you don’t. However, I want to use SSL profiles, as they allow way more stream-lined SSL handling. At the same time, I wanted to be able to use TLS 1.3 as well. Following CTX259045, we have to change the way, SSL/TLS is handled by Citrix ADC / NetScaler. This may lead to temporarily degraded security of existing SSL vServers! So I recommend taking a moment before proceeding! Read on, have a cup of coffee and try to understand the risk, than do.
The reason is: If you use SSL profiles, Citrix ADC / NetScaler will not allow TLS 1.3. It would work, if you don’t. However, I want to use SSL profiles, as they allow way more stream-lined SSL handling. At the same time, I wanted to be able to use TLS 1.3 as well. Following CTX259045, we have to change the way, SSL/TLS is handled by Citrix ADC / NetScaler. This may lead to temporarily degraded security of existing SSL vServers! So I recommend taking a moment before proceeding! Read on, have a cup of coffee and try to understand the risk, than do.
There is a tool to convert an ns.conf file to default profile. It’s freely available for Windows, Linux and MacOS from GitHub.
The impact on existing vServers
We have to change an SSL parameter and because of this, all SSL vServers get reverted to the default SSL profile ns_default_ssl_profile_frontend. It will get the DEFAULT cypher group assigned. Grade in SSL Labs will (currently) temporarely get cut to B or even C.
So changing the SSL parameter has to be well-planned!
I am quoting Citrix:
NOTE: When the command ‘setssl parameter -defaultProfile E‘ is executed, the Enhanced SSL profile settings will override the existing SSL profile settings bound on the Vserver as well as on the Vservice. Hence, take a backup of existing configuration before executing the above command. So that, customer can check the ns.conf and manually edit the SSL profile settings of specific Vserver with required parameters.
Actually, that’s not precise. It does not overwrite but replaces existing profiles with the default profile. The original profiles still exist and all their settings got preserved. So we can reassign these profiles after setting them correctly.
 Attention!
Attention!
Enabling default profiles is a one-way procedure. There is no way back! The only way to undo this change is a reboot (before saving the configuration)
Changing SSL Parameters
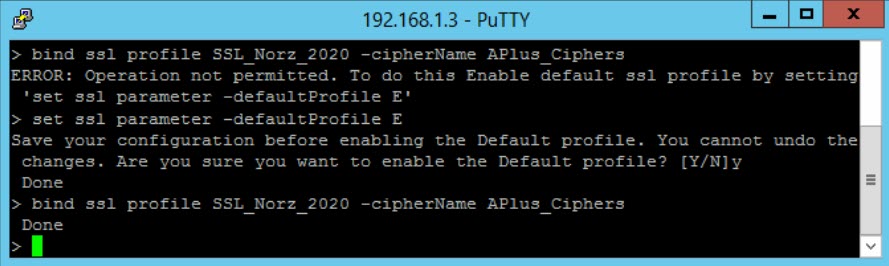
Binding Cypher groups to an SSL profile will fail, unless we change the SSL parameter “Default profile” to E
set ssl parameter -defaultProfile E
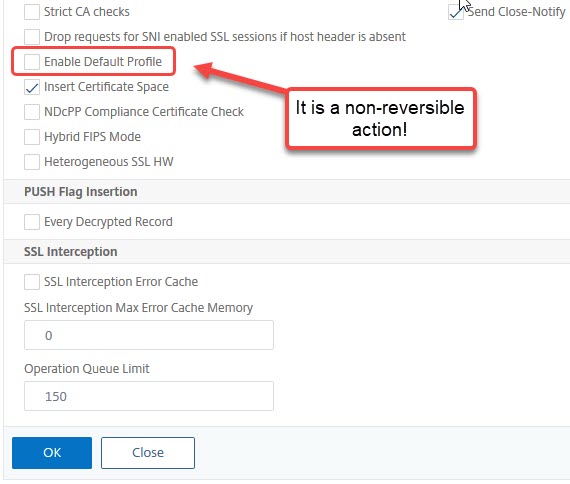
Like mentioned above, this will change everything about SSL. It’s non-reversible. But from now on, we are able to bind cypher groups to SSL profiles (just now, this rather insecure DEFAULT profile is bound to all existing SSL-profiles).
Cyphers to use
I discussed cypher groups precisely, so I skip this here. I just give a Citrix ADC / NetScaler command to create a cyphers group currently scoring an A+ in SSL labs.
 Keep in Mind:
Keep in Mind:
“The best” Cypher groups don’t exist. Security recommendations are constantly changing. So don’t trust my list! It had been a good list in December 2020, it may be a horrible one right now!
Keep testing and testing and testing!
As I discussed there, these suggestions are for browser-based access only. Citrix Workspace App just supports a very limited set of cyphers!
add ssl cipher APlus_Ciphers
#in case you don't use WorkSpace App. It does not support ChaCha cyphers:
bind ssl cipher APlus_Ciphers -cipherName TLS1.3-CHACHA20-POLY1305-SHA256 -cipherPriority 16
bind ssl cipher APlus_Ciphers -cipherName TLS1.3-AES256-GCM-SHA384 -cipherPriority 32
bind ssl cipher APlus_Ciphers -cipherName TLS1.3-AES128-GCM-SHA256 -cipherPriority 48
bind ssl cipher APlus_Ciphers -cipherName TLS1.2-ECDHE-RSA-CHACHA20-POLY1305 -cipherPriority 64
#in case you don't use WorkSpace App. It does not support ChaCha cyphers:
bind ssl cipher APlus_Ciphers -cipherName TLS1.2-DHE-RSA-CHACHA20-POLY1305 -cipherPriority 80
bind ssl cipher APlus_Ciphers -cipherName TLS1.2-ECDHE-RSA-AES256-GCM-SHA384 -cipherPriority 96
bind ssl cipher APlus_Ciphers -cipherName TLS1.2-DHE-RSA-AES256-GCM-SHA384 -cipherPriority 112
bind ssl cipher APlus_Ciphers -cipherName TLS1.2-ECDHE-RSA-AES128-GCM-SHA256 -cipherPriority 128
The Citrix ADC / NetScaler SSL Profile
The SSL profile needed is not that different from a TLS 1.2 profile, except the cypher group bound to it and the setting enabling TLS 1.3.
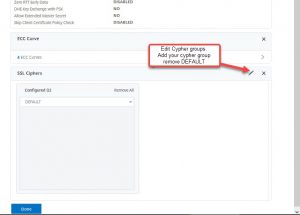
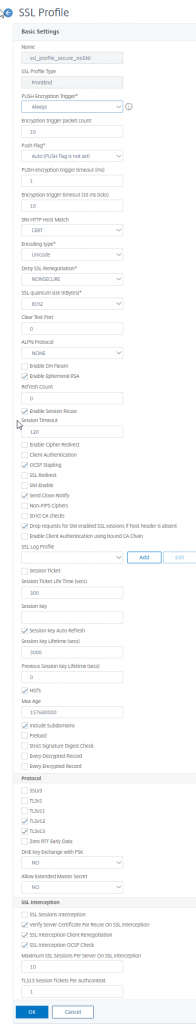 Next, we have to bind the right cypher group and un-bind DEFAULT cyphers.
Next, we have to bind the right cypher group and un-bind DEFAULT cyphers.
That’s it! Go to SSL labs SSL test and test your deployment. Don’t forget to also test all other vServers that are currently existing on your Citrix ADC (NetScaler)!
Any suggestion and comment would be highly welcome!