This is the forth part of this blog. Part Part 1 2 3 4 5
I am currently working on a Citrix ADC (NetScaler) WAF project. It’s a big international enterprise, security is of some concern to them. So everything hould be pretty much straight forward?
Well, it never is. So, how to begin?
Well, I almost forgot to mention: I have to introduce myself to the customer. “Hi, I’m Johannes, and I will do false positives“. I will do for sure. Everyone does. Not because I’m too stupid, but because I usually can’t get all information needed, so things will go wrong for sure. It’s just to set the expectation to a proper level.
First task: Do an inventory
The hardware
My customer already had their Citrix ADCs in place. It’s some ADCs each supporting a bunch of apps, running on a pair of SDX 14,000 appliances.
My first step is doing a performance baseline. How much CPU load do these boxes show? I wrote down the numbers, both per VPX and for the SDX. About the SDX: If some VPX share a CPU you have to do considder the worst case, so move all of them to the same box. My customer’s ADCs run on far less than 20% peak CPU load, so I dont see any problems about the CPUs looming behind the horizon. Keep in mind: WAF is mainly about the CPU!
The applications
Next, important, step: Which applications have to be protected? There is a shore number of questions, I’m always using:
- Do you consider this application to be on high risk (usually all of them are) and how sensitive is the data
- What kind of data is it (so I can get an idea about how accurate the previous answer had been)
- Which lb/cs vServer is responsible for this app?
- Which operating system is the server using?
- Which tools and frameworks does this application use? PHP, CGI, … Ruby, WordPress, …
- Does the application use a data base? Which kind of data base?
- Does it use any other back-end resources like MS Exchange, MS Sharepoint
- Does the app use XML, YAML or SOAP?
- Did they write the application themselves or did they buy it?
- How quick can this application get patched?
- Who is responsible for this application?
- Can I get access to the application? (Dosn’t make sense for complex ones as I’m stupid like fuck if it comes to commercial tasks. Because of this I can’t deal with SAP and similar highly complex apps, but became a network engineer)Can I get access to the application? (Doesn’t make sense for complex ones as I’m stupid like fuck. I can’t deal with SAP and similar apps)
- Does this application store sensitive data that must not be exposed to the public, even in case of the application being crashed (credit cards, …)
Well, you’ll very soon find out: The answer to question 4, 5, 6, 7 and 10 will be not what you expected. Instead there will be none or tf you get an answer it will be rather vague or even a rough estimation.
Technical prerequisites
I need to be full ADC admin, as I need access to bash. And hey, I’m not a masochist, so don’t even mention the “CLI” in the GUI! I need access on port 443 (80) and 22. It’s not possible without.
First steps
First things first: I do most of the work from the GUI. Just because it’s way more handy. There is much assistance from the GUI as well.
As a first step, I will google if there is an implementation guide for this specific application and if there are well known issues.
Second, I usually create a profile. I use a strict naming convention and capital letters, I want to be able to use grep to find certain records and am not interested in false positives! My personal naming convention is APPFWP_NAME_OF_THE_APPLICATION. It’s very unlikely for other objects and log data to contain strings like that, so it can’t be mixed up with anything else.
There are two things to decide (or, to be true, just one):
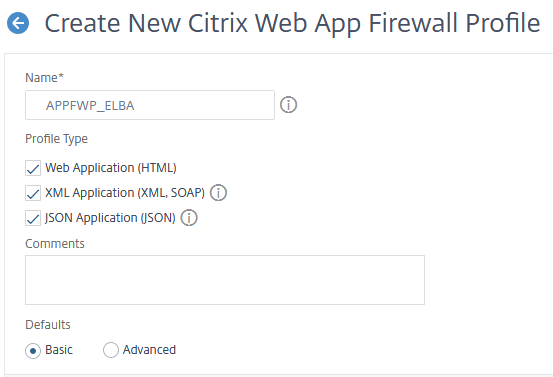 So the question here is: Does the application use HTML, XML or SOAP. I hope you already know. Just tick the ones you need. If you don’t know: Select all of them! You may change this later (click the 3 dots next to the profile and select “change profile type”).
So the question here is: Does the application use HTML, XML or SOAP. I hope you already know. Just tick the ones you need. If you don’t know: Select all of them! You may change this later (click the 3 dots next to the profile and select “change profile type”).
The second question is no question at all: Basic or Advanced is just about which checks are pre-enabled. I always go with basic, so I don’t have too much work to do disabling all checks…
continue reading about how to create signatures signatures
